Government Security News (GSN) just published an article (http://www.gsnmagazine.com/node/27833?c=infrastructure_protection) about the recent declassification of documents identifying that our electric grid is still vulnerable to terrorist attacks. Really? I’m not sure there needed to be a classified document in the first place. The vulnerability of our grid should be pretty obvious.
The report was focused on the vulnerabilities to terrorist attacks – but thankfully did at least acknowledge that impacts can be caused by natural disasters (by the way, the lights are still out on Long Island). Terrorist vulnerabilities absolutely do exist, though. Our energy infrastructure is very open, physically and virtually. Generally, power generation facilities have decent security – particularly nuclear power plants. Security does drop notably with other facilities, especially hydro-generation plants, which should have the same measure of security as nuclear power plants as most of them are associated with a dam, which, if breached not only knocks out power generation but also is bound to impact a population catastrophically.
Most energy sub-stations are not staffed, and while there is passive security in place, such as fencing, these can obviously be overcome easily. Utility lines stretch across our nation above and below ground – generally accessible with little trouble to people with malicious intent. Remember that acts interrupting our grid may not necessarily come from Al-Qaeda, but can come from disgruntled locals as well. Take a look at the pictures below. These were actually taken by my father who worked for a utility company in New York State. Shortly after these high power transmission lines were put up over 25 years ago, a local, in protest over these lines going through their land, actually unbolted the tower from the base. They never caught the person who did it – but this is a federal crime – and taken very seriously by prosecutors and law enforcement, including security personnel of the utility companies. This same transmission line passes through my property and my family and I have made several calls through the years to the security office of the utility company when we see people loitering around and taking pictures or notes on these towers.



In consideration of cyber attacks – guess what – they happen EVERY DAY! Most, fortunately, are pretty weak and stopped well short of their goal. Some do have some measure of success, penetrating fire walls and other defenses. Some come from individuals domestically, but many are known to come from the likes of China, North Korea, and Iran – all of which ‘officially’ deny sponsoring such acts of terrorism. Practically everything is controlled by a computer, and practically every computer is networked and accessible from the outside world by people who know how to do so. Energy plants can be shut down, overloaded, or have safety protocols circumvented. Scary stuff.
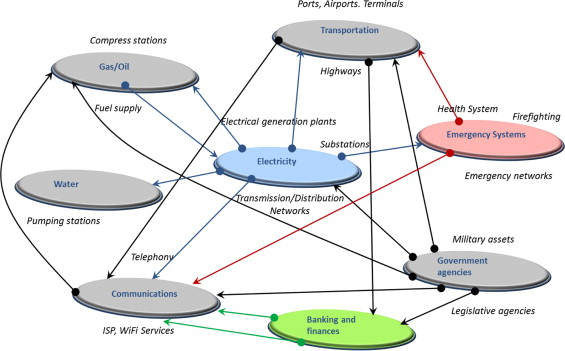
So what’s the result of all this? Much more than the inconvenience of a short-term power outage, I can assure you of that. Our energy grid is the most critical of our infrastructure. Without it nothing works. We’ve only scratched the surface of examples from the areas that were hit by Hurricane Sandy and still don’t yet have power. It impacts our other critical infrastructures such as communications, hospitals, the economy, and others. It breaks beyond discomfort and inconvenience when it endangers lives during periods of temperature extremes. All in all we have an aging infrastructure in our nation, but not only do we need to work on replacing and improving it, we need to protect it.